Are you interested in a career in cybersecurity or simply passionate about exploring the field? A home lab is one of the best ways to develop hands-on skills and deepen your knowledge in a controlled and safe environment. Designed to simulate real-world scenarios, a home lab helps you practice both attacking and defending systems, preparing you for the challenges you’ll encounter in the cybersecurity landscape.
This guide will provide an in-depth look at the essential components you’ll need to build a home lab for cybersecurity, along with tips for setting it up successfully. Buckle up—your cybersecurity adventure starts here.
What is a Home Lab and Why Is It Important?
A home lab serves as a sandbox environment where aspiring cybersecurity professionals or enthusiasts can safely experiment, learn, and practice. It removes the risk of testing on live systems while giving you the flexibility to replicate various network setups and scenarios. Whether you’re interested in penetration testing, ethical hacking, or network defense, a home lab is your training ground to gain practical experience.
But before you get started, you’ll need specific tools, software, and equipment to set up your lab. Let’s break them down step by step.
1. Virtualization Software: The Backbone of Your Lab
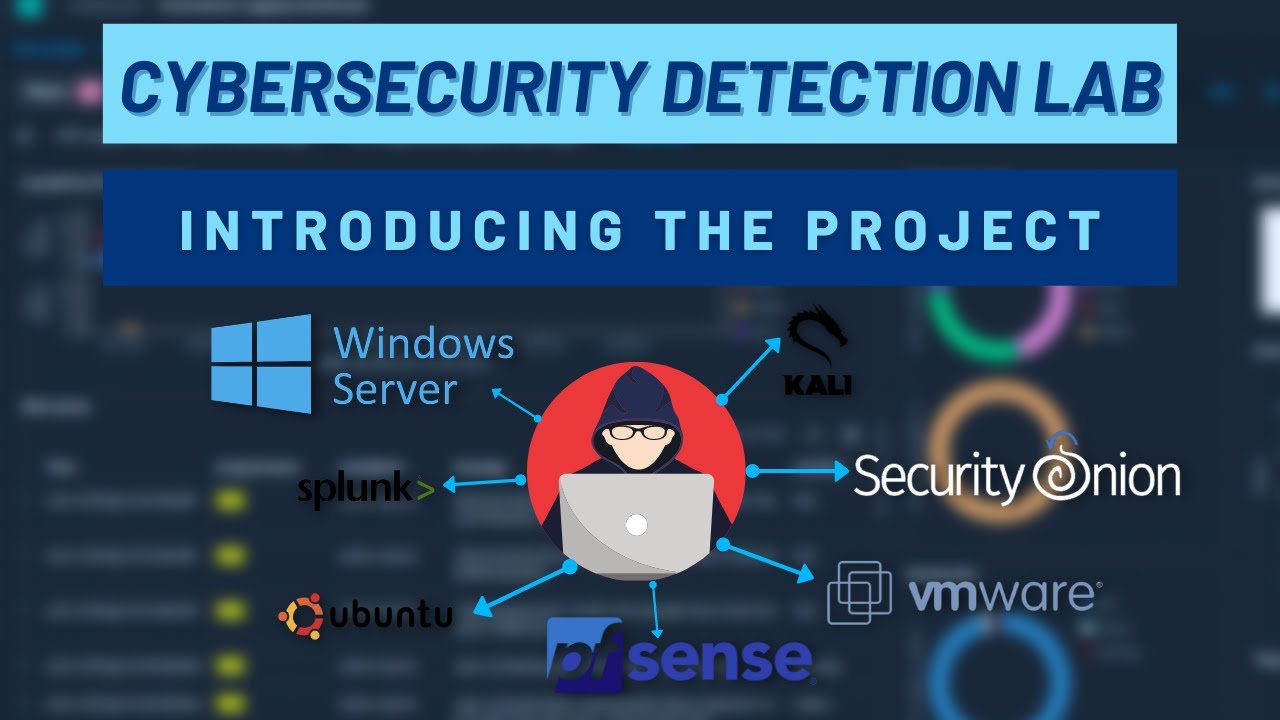
Virtualization software is the foundation of any home lab. It lets you run multiple virtual machines (VMs) on a single physical computer, essentially allowing one computer to act like many. This flexibility is crucial for simulating networks and testing different configurations.
Recommended Virtualization Tools
- VirtualBox (Free and open-source)
- VMware Workstation Player (Free for personal use; Pro version available with more features)
- Hyper-V (Built into Windows 10 Pro and Enterprise editions)
With virtualization software, you can install various operating systems and applications on your virtual machines, creating isolated environments for hands-on learning.
2. Operating Systems to Include in Your Lab
To maximize your learning, install a mix of operating systems to simulate diverse scenarios and vulnerabilities. Different platforms have unique security challenges, and understanding how they work is crucial in your cybersecurity training.
Must-Have Operating Systems
- Windows (e.g., Windows 10/11): Widely used in businesses, making it essential for practicing defending workstations and servers.
- Linux Distributions: Popular options include Ubuntu, Kali Linux (for penetration testing), and Fedora. Kali Linux, in particular, is a staple for those interested in ethical hacking.
- macOS (if available): Though less commonly targeted, it’s valuable for testing compatibility and gaining insights into its security ecosystem.
Having this variety of operating systems ensures you’re well-versed in handling threats across multiple platforms.
3. Essential Tools and Software for Cybersecurity Practice
The tools you use in your home lab will play a significant role in developing your skills. Here’s a breakdown of some key categories and recommended software/tools for each.
Penetration Testing Tools
Practicing penetration testing helps sharpen your ability to identify and exploit vulnerabilities—skills highly sought after in the industry.
- Metasploit Framework
- Nmap
- Aircrack-ng
- John the Ripper
Vulnerability Scanners
Vulnerability scanners locate and assess weaknesses within a system or network.
- Nessus
- OpenVAS
- QualysGuard
Security Information and Event Management (SIEM) Software
SIEM tools monitor, analyze, and log security events, making them invaluable for learning network defense strategies.
- Splunk
- Elastic Stack (formerly ELK Stack)
- Graylog
Firewalls
Firewalls form the basis of network security. Explore configuring and managing these in your lab.
- pfSense
- Untangle
- Sophos UTM
A combination of these tools will give you the breadth and depth of skills you need.
4. Networking Equipment for Real-World Simulations
To create a realistic network environment, you’ll need the right networking equipment. While virtualization can simulate many networking features, physical equipment offers additional learning opportunities.
Recommended Networking Hardware
- Routers
- Switches
- Network Adapters
- Firewalls
This equipment allows you to practice configuring complex network setups, monitoring traffic, and testing attack scenarios in a simulated environment.
5. Importance of Sufficient Storage Space
Working with virtualization and large data sets often requires significant storage space. A fast and reliable solid-state drive (SSD) is recommended to store your virtual machines and operating systems, ensuring quick performance and minimal downtime.
Consider an SSD with at least 500GB or more to accommodate your growing lab. Additionally, external drives can help expand your storage capacity when needed.
Steps to Build and Maximize Your Home Lab
Now that you know what you need, here’s how to put it all together:
- Plan Your Setup
- Decide what tools, operating systems, and equipment fit your goals.
- Install Virtualization Software
- Set up and configure your virtualization tool of choice.
- Create Virtual Machines
- Install multiple operating systems, ensuring to allocate sufficient resources (CPU, RAM, storage) to each.
- Install Cybersecurity Tools
- Download and configure open-source and commercial tools for practice.
- Simulate a Network Environment
- Use your networking equipment or virtualized networks to replicate a real-world setup.
- Experiment Safely
- Practice penetration testing, vulnerability scanning, and network defense—all within your controlled environment.
Benefits of Building a Home Lab for Cybersecurity
Creating a home lab offers countless benefits:
- Hands-On Training: Theory only gets you so far; a home lab provides the hands-on experience employers value most.
- Skill Development: Practice key skills like ethical hacking, network defense, and incident response.
- Safe Learning Environment: Experimentation in your lab carries no real-world risks.
- Flexible Learning: Tinker and learn at your own pace, tailoring the experience to your interests and career goals.
Final Thoughts
If you’re passionate about cybersecurity, a home lab is an invaluable investment in your future. Whether you’re just getting started or looking to advance your skills, having the right tools and resources at your fingertips will help you excel in this dynamic field.
Take the first step today—start setting up your cybersecurity home lab, and get ready to unlock your full potential. Happy learning!